C Y B E R S E C U R I T Y
applications should always have the latest
security patches.”
Staff training is just as important as
securing critical systems. Human error was
the cause of roughly 90% of data breaches
reported to the Information Commissioner’s
Office (ICO) in the UK between 2017 and
2018. All personnel should be aware of the
risks if they don’t follow good practices in
their daily activities.
“Training is absolutely key to
cybersecurity,” says Cowan. “People have
to know their responsibilities. If there is
a cyber attack they need to know how
they should respond and who they should
report it to. There are some great specialist
cybersecurity training providers out there
now – I’ve come across several specialists
through my work with the London Office for
Rapid Cybersecurity Advancement.”
Anton also recommends organizations
implement an appropriate cybersecurity
management system. Aspects that it
should cover include: a clear definition
of responsibilities within the organization,
identification of safety critical activities,
facilities, equipment and systems,
identification of interfaces with other
organizations that share cybersecurity risks,
the performance of risk assessments and
development of mitigation measures.
Work together, not alone
Aviation is a system-of-systems with a
constantly increasing interconnection
between different organizations, products
and systems. As a consequence,
cybersecurity events affecting one
organization will affect other organizations
and eventually may have an impact on the
“Access to information and
systems should be locked down
so that only authorized users
can access them.”
44 | BU S INE S S A I R P O R T INT E RNAT I ONA L J U L Y 2 0 1 9
safe operation of the aircraft, even if such
aircraft has been certified following very
strict requirements.
This means that it’s not possible for
organizations to address cybersecurity risks
alone. The global nature of aviation means
it is key that organizations around the world
come together to address the risks they face
and promote. EASA is working towards “the
harmonization of regulatory requirements,”
says Anton, something that EASA practices
regarding the development of the EU
aviation cybersecurity strategy. EASA is
also working closely with the International
Civil Aviation Organization (ICAO) with the
objective of developing a global aviation
cybersecurity strategy.
Cowan believes aviation operators and
infrastructure providers and suppliers need
to work closer on the continued protection
of systems. “Attitudes need to change,”
he says. “Currently, once a
company has supplied a
piece of equipment, they
say their work is done.
They’re not forced to ensure a
system is updated or patched, that’s
down to the customer. This is
changing though thanks to new
rules in commercial aviation.
“Discussions also need
to be had around asset
management. Security doesn’t
just happen once. It’s a
continuous process as risks
change and new vulnerabilities
appear over time. Decisions need
to be made around who’s responsible
for ensuring a product remains secure,”
he concludes.
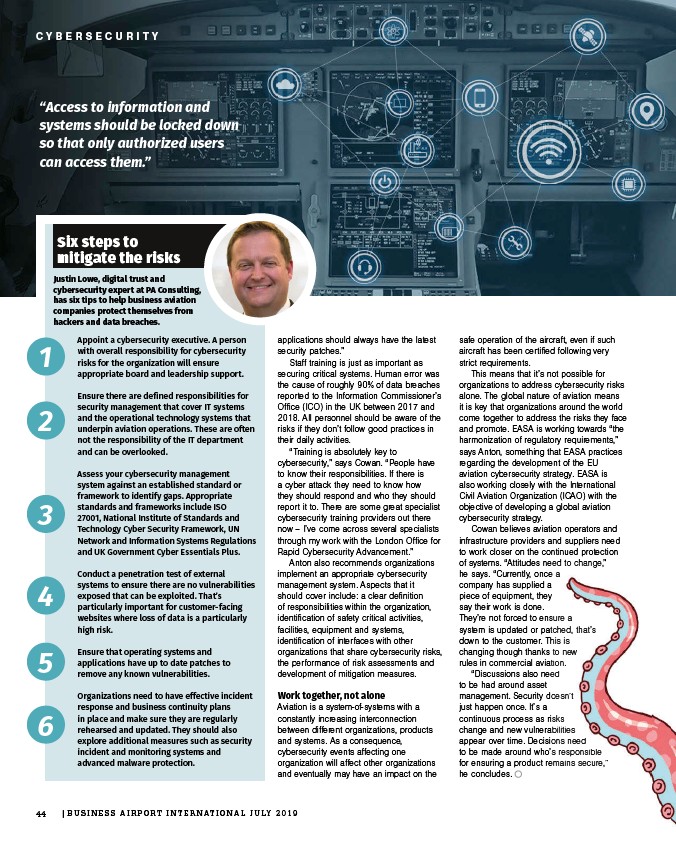
Six steps to
mitigate the risks
Justin Lowe, digital trust and
cybersecurity expert at PA Consulting,
has six tips to help business aviation
companies protect themselves from
hackers and data breaches.
Appoint a cybersecurity executive. A person
with overall responsibility for cybersecurity
risks for the organization will ensure
appropriate board and leadership support.
Ensure there are defined responsibilities for
security management that cover IT systems
and the operational technology systems that
underpin aviation operations. These are often
not the responsibility of the IT department
and can be overlooked.
Assess your cybersecurity management
system against an established standard or
framework to identify gaps. Appropriate
standards and frameworks include ISO
27001, National Institute of Standards and
Technology Cyber Security Framework, UN
Network and Information Systems Regulations
and UK Government Cyber Essentials Plus.
Conduct a penetration test of external
systems to ensure there are no vulnerabilities
exposed that can be exploited. That’s
particularly important for customer-facing
websites where loss of data is a particularly
high risk.
Ensure that operating systems and
applications have up to date patches to
remove any known vulnerabilities.
Organizations need to have effective incident
response and business continuity plans
in place and make sure they are regularly
rehearsed and updated. They should also
explore additional measures such as security
incident and monitoring systems and
advanced malware protection.
1
2
3
4
5
6